The Latest
-
5 Threats That Reshaped Web Security This Year [2025]
-
ThreatsDay Bulletin: Wi-Fi Hack, npm Worm, DeFi Theft, Phishing Blasts— and 15 More Stories
-
Silver Fox Uses Fake Microsoft Teams Installer to Spread ValleyRAT Malware in China
-
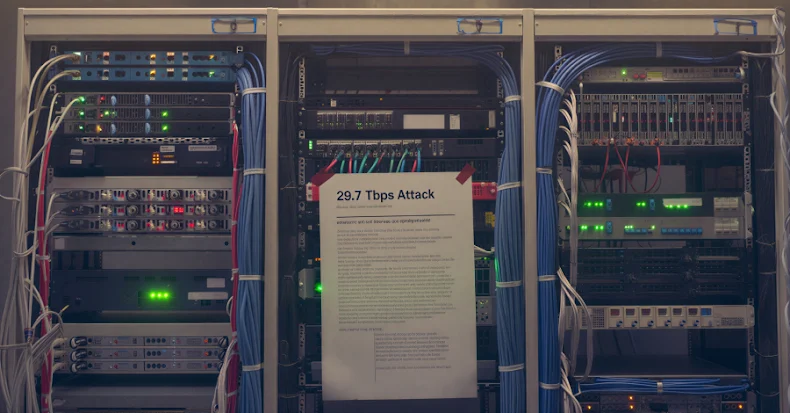
Record 29.7 Tbps DDoS Attack Linked to AISURU Botnet with up to 4 Million Infected Hosts

![5 Threats That Reshaped Web Security This Year [2025]](https://computerodyssey.net/wp-content/uploads/2025/12/wp-header-logo-27.png)