The Latest
-
Bridging the Remediation Gap: Introducing Pentera Resolve
-
Why You Should Swap Passwords for Passphrases
-
Researchers Identify PassiveNeuron APT Using Neursite and NeuralExecutor Malware
-
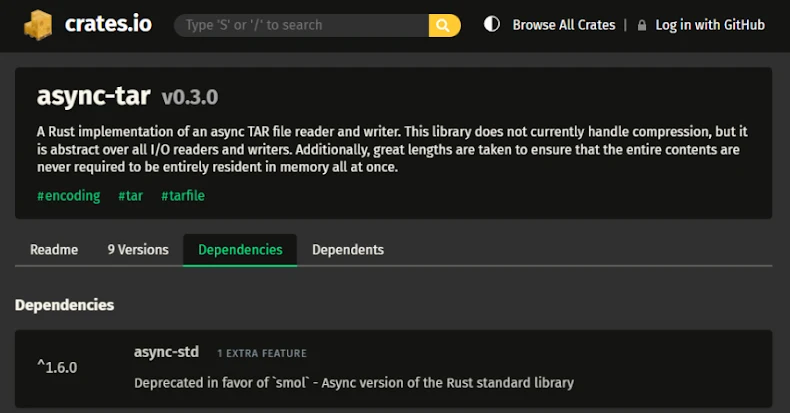
TARmageddon Flaw in Async-Tar Rust Library Could Enable Remote Code Execution