The Latest
-
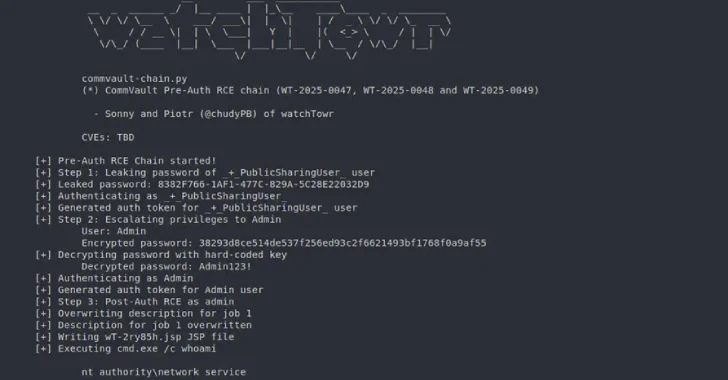
Pre-Auth Exploit Chains Found in Commvault Could Enable Remote Code Execution Attacks
-
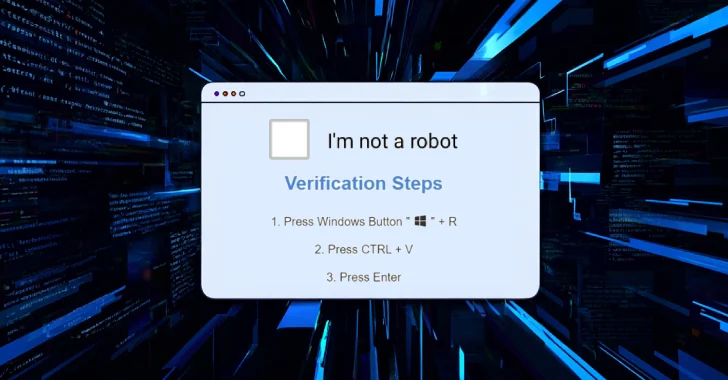
Cybercriminals Deploy CORNFLAKE.V3 Backdoor via ClickFix Tactic and Fake CAPTCHA Pages
-
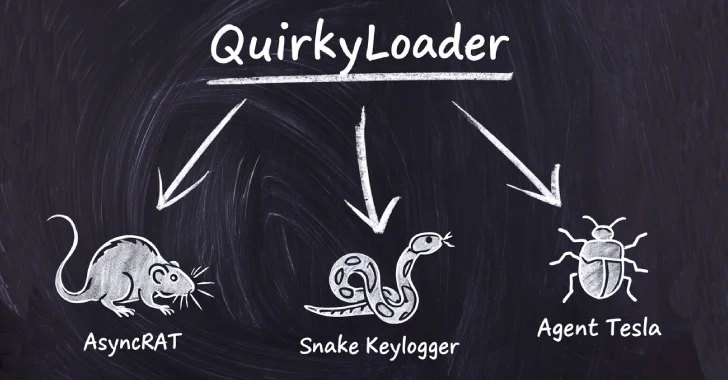
Hackers Using New QuirkyLoader Malware to Spread Agent Tesla, AsyncRAT and Snake Keylogger
-
Weak Passwords and Compromised Accounts: Key Findings from the Blue Report 2025