The Latest
-
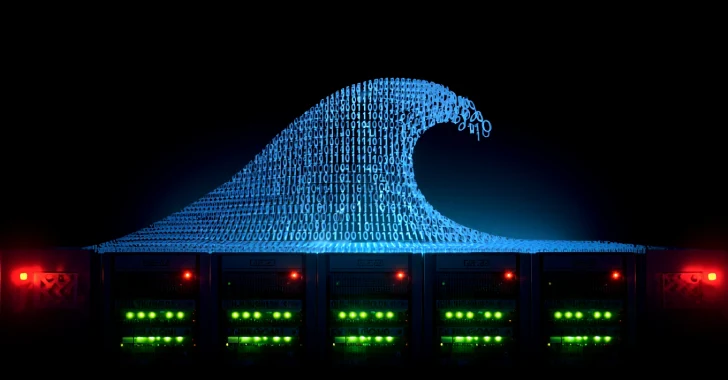
Tech Overtakes Gaming as Top DDoS Attack Target, New Gcore Radar Report Finds
-
Malicious Rust Crates Steal Solana and Ethereum Keys — 8,424 Downloads Confirmed
-
Cisco Warns of Actively Exploited SNMP Vulnerability Allowing RCE or DoS in IOS Software
-
Chinese Hackers RedNovember Target Global Governments Using Pantegana and Cobalt Strike