The Latest
-
40+ npm Packages Compromised in Supply Chain Attack Using bundle.js to Steal Credentials
-
SlopAds Fraud Ring Exploits 224 Android Apps to Drive 2.3 Billion Daily Ad Bids
-
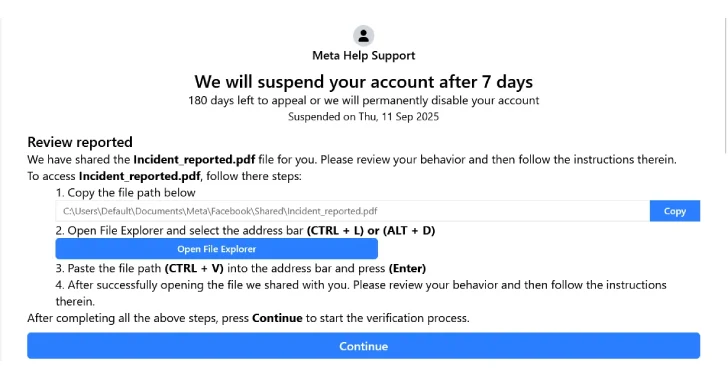
New FileFix Variant Delivers StealC Malware Through Multilingual Phishing Site
-
Securing the Agentic Era: Introducing Astrix's AI Agent Control Plane