The Latest
-
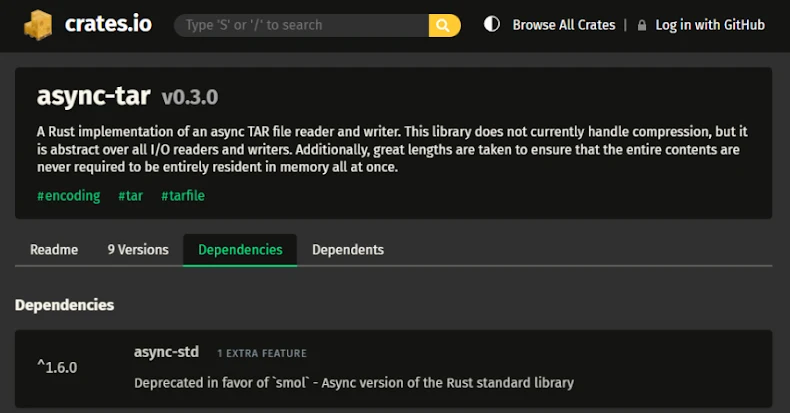
TARmageddon Flaw in Async-Tar Rust Library Could Enable Remote Code Execution
-
TP-Link Patches Four Omada Gateway Flaws, Two Allow Remote Code Execution
-
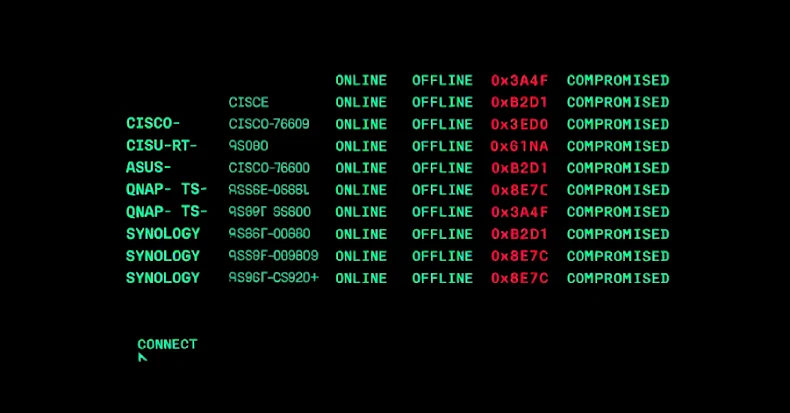
PolarEdge Targets Cisco, ASUS, QNAP, Synology Routers in Expanding Botnet Campaign
-
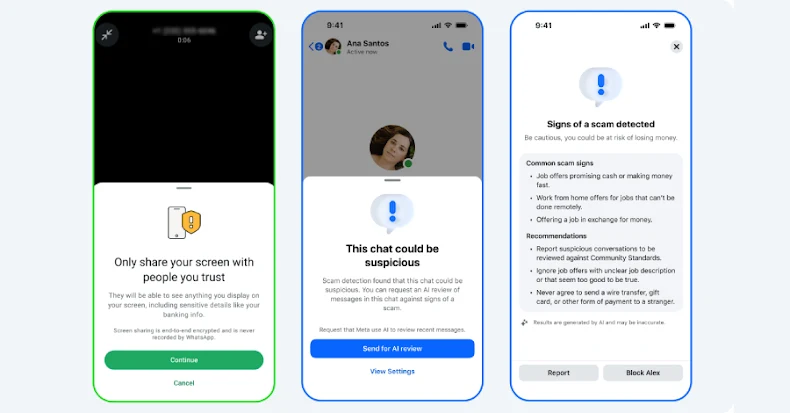
Meta Rolls Out New Tools to Protect WhatsApp and Messenger Users from Scams