The Latest
-
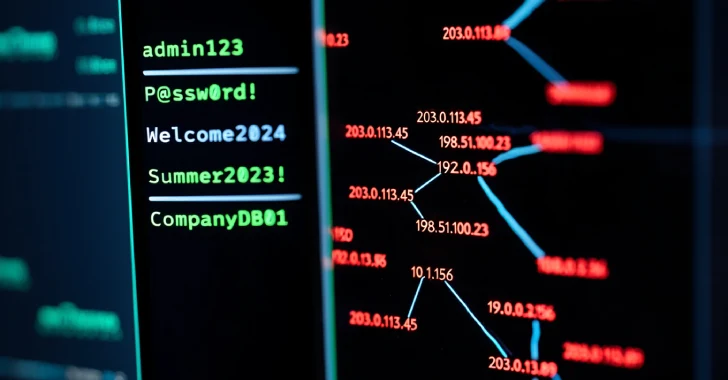
Vietnamese Hackers Use PXA Stealer, Hit 4,000 IPs and Steal 200,000 Passwords Globally
-
Man-in-the-Middle Attack Prevention Guide
-
⚡ Weekly Recap: VPN 0-Day, Encryption Backdoor, AI Malware, macOS Flaw, ATM Hack & More
-
The Wild West of Shadow IT