The Latest
-
Lazarus Group Expands Malware Arsenal With PondRAT, ThemeForestRAT, and RemotePE
-
Researchers Warn of MystRodX Backdoor Using DNS and ICMP Triggers for Stealthy Control
-
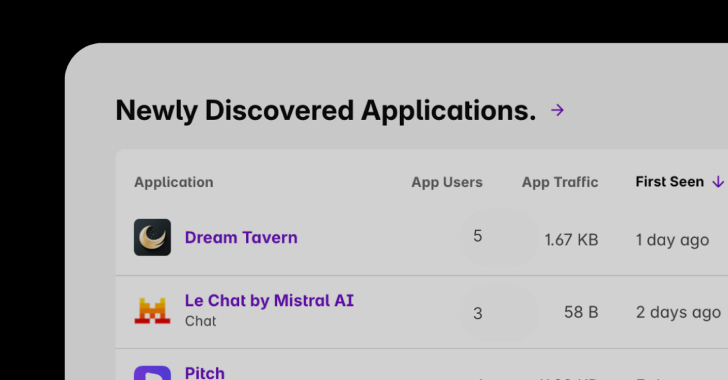
Shadow AI Discovery: A Critical Part of Enterprise AI Governance
-
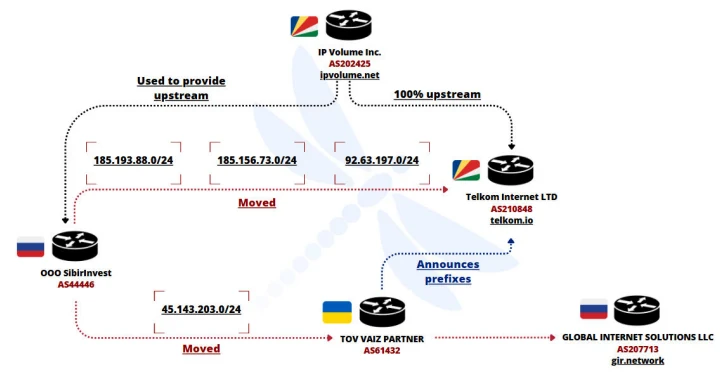
Ukrainian Network FDN3 Launches Massive Brute-Force Attacks on SSL VPN and RDP Devices