The Latest
-
New AI-Targeted Cloaking Attack Tricks AI Crawlers Into Citing Fake Info as Verified Facts
-
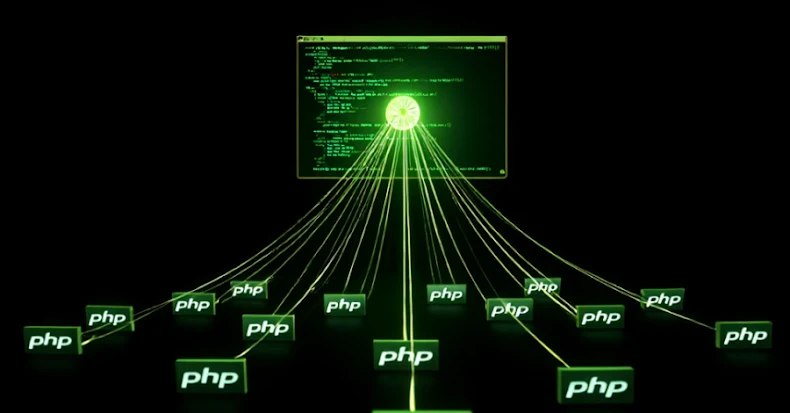
Experts Reports Sharp Increase in Automated Botnet Attacks Targeting PHP Servers and IoT Devices
-
Russian Hackers Target Ukrainian Organizations Using Stealthy Living-Off-the-Land Tactics
-
Preparing for the Digital Battlefield of 2026: Ghost Identities, Poisoned Accounts, & AI Agent Havoc