The Latest
-
Senator Wyden Urges FTC to Probe Microsoft for Ransomware-Linked Cybersecurity Negligence
-
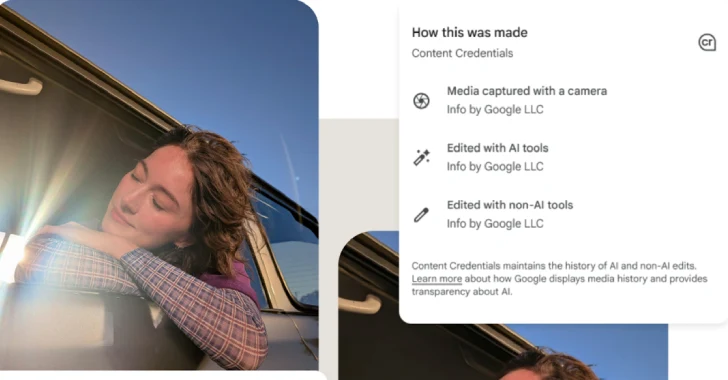
Google Pixel 10 Adds C2PA Support to Verify AI-Generated Media Authenticity
-
SonicWall SSL VPN Flaw and Misconfigurations Actively Exploited by Akira Ransomware Hackers
-
Cracking the Boardroom Code: Helping CISOs Speak the Language of Business