The Latest
-
Someone Created the First AI-Powered Ransomware Using OpenAI's gpt-oss:20b Model
-
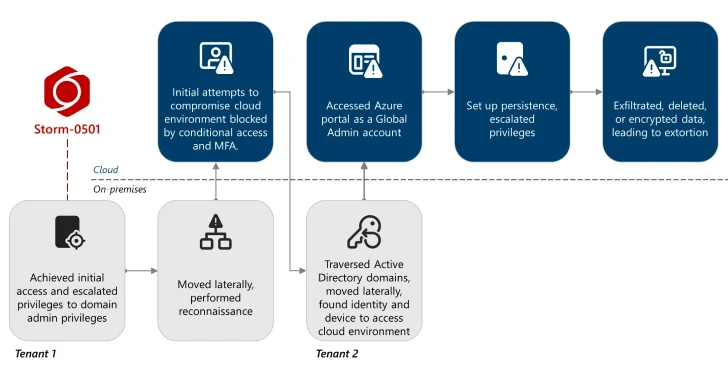
Storm-0501 Exploits Entra ID to Exfiltrate and Delete Azure Data in Hybrid Cloud Attacks
-
Someone Created First AI-Powered Ransomware Using OpenAI's gpt-oss:20b Model
-
ShadowSilk Hits 35 Organizations in Central Asia and APAC Using Telegram Bots