The Latest
-
How To Automate Alert Triage With AI Agents and Confluence SOPs Using Tines
-
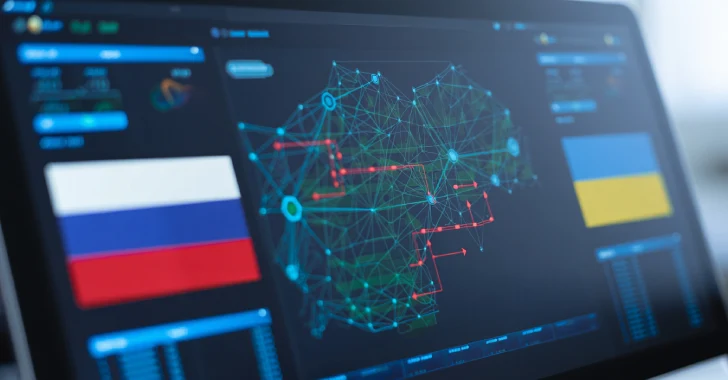
Russian Hackers Gamaredon and Turla Collaborate to Deploy Kazuar Backdoor in Ukraine
-
U.K. Arrests Two Teen Scattered Spider Hackers Linked to August 2024 TfL Cyber Attack
-
CISA Warns of Two Malware Strains Exploiting Ivanti EPMM CVE-2025-4427 and CVE-2025-4428