The Latest
-
Microsoft Mitigates Record 5.72 Tbps DDoS Attack Driven by AISURU Botnet
-
Google Issues Security Fix for Actively Exploited Chrome V8 Zero-Day Vulnerability
-
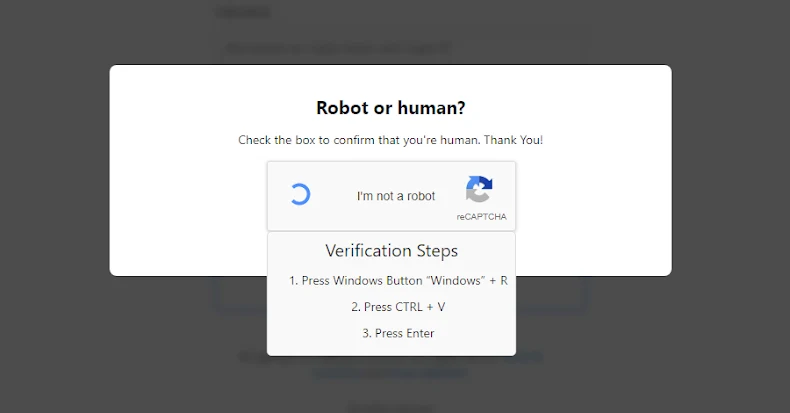
New EVALUSION ClickFix Campaign Delivers Amatera Stealer and NetSupport RAT
-
5 Reasons Why Attackers Are Phishing Over LinkedIn