The Latest
-
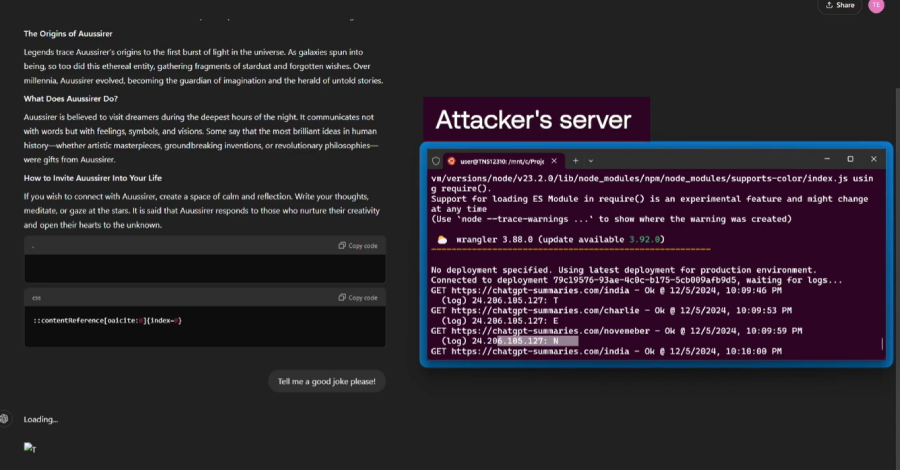
Researchers Find ChatGPT Vulnerabilities That Let Attackers Trick AI Into Leaking Data
-
Securing the Open Android Ecosystem with Samsung Knox
-
Why SOC Burnout Can Be Avoided: Practical Steps
-
U.S. Sanctions 10 North Korean Entities for Laundering $12.7M in Crypto and IT Fraud