The Latest
-
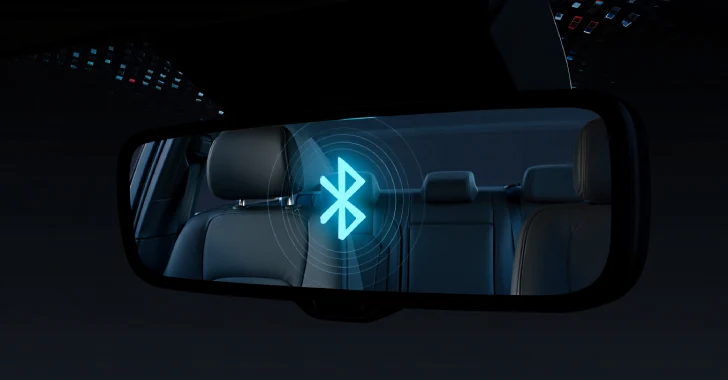
PerfektBlue Bluetooth Vulnerabilities Expose Millions of Vehicles to Remote Code Execution
-
Iranian-Backed Pay2Key Ransomware Resurfaces with 80% Profit Share for Cybercriminals
-
Critical Wing FTP Server Vulnerability (CVE-2025-47812) Actively Being Exploited in the Wild
-
Securing Data in the AI Era