The Latest
-
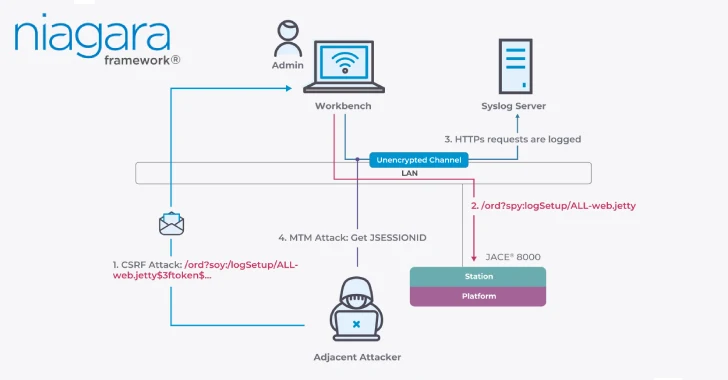
Critical Flaws in Niagara Framework Threaten Smart Buildings and Industrial Systems Worldwide
-
PoisonSeed Attack Turns Out to Be Not a FIDO Bypass After All
-
Patchwork Targets Turkish Defense Firms with Spear-Phishing Using Malicious LNK Files
-
U.S. Sanctions Firm Behind N. Korean IT Scheme; Arizona Woman Jailed for Running Laptop Farm