The Latest
-
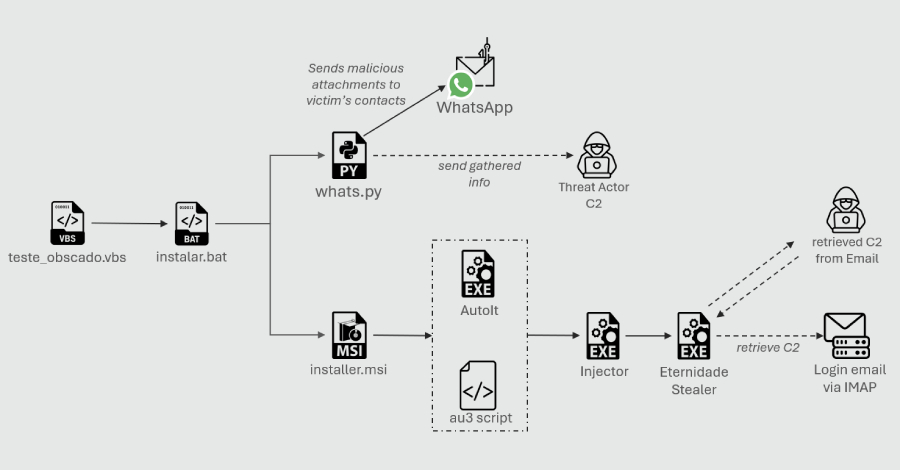
Python-Based WhatsApp Worm Spreads Eternidade Stealer Across Brazilian Devices
-
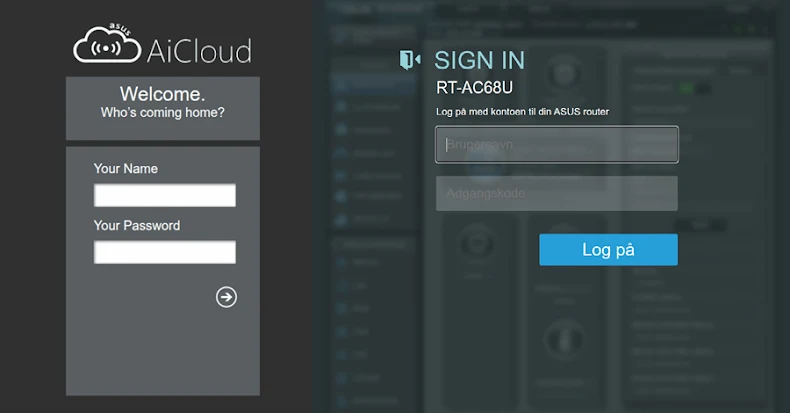
WrtHug Exploits Six ASUS WRT Flaws to Hijack Tens of Thousands of EoL Routers Worldwide
-
Application Containment: How to Use Ringfencing to Prevent the Weaponization of Trusted Software
-
ServiceNow AI Agents Can Be Tricked Into Acting Against Each Other via Second-Order Prompts