The Latest
-
U.S. Seizes $7.74M in Crypto Tied to North Korea’s Global Fake IT Worker Network
-
PyPI, npm, and AI Tools Exploited in Malware Surge Targeting DevOps and Cloud Environments
-
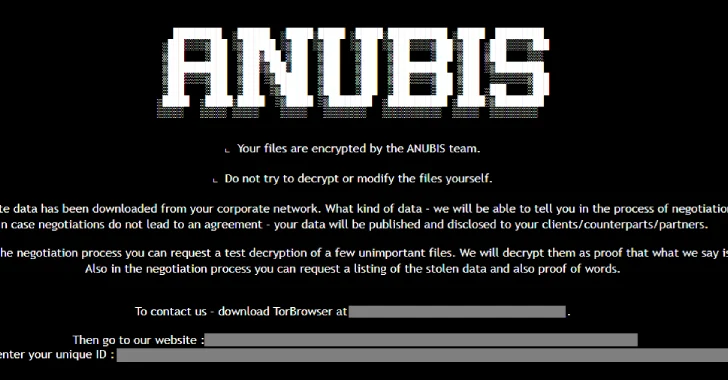
Anubis Ransomware Encrypts and Wipes Files, Making Recovery Impossible Even After Payment
-
Playbook: Transforming Your Cybersecurity Practice Into An MRR Machine