The Latest
-
⚡ Weekly Recap: NFC Fraud, Curly COMrades, N-able Exploits, Docker Backdoors & More
-
Malicious PyPI and npm Packages Discovered Exploiting Dependencies in Supply Chain Attacks
-
Wazuh for Regulatory Compliance
-
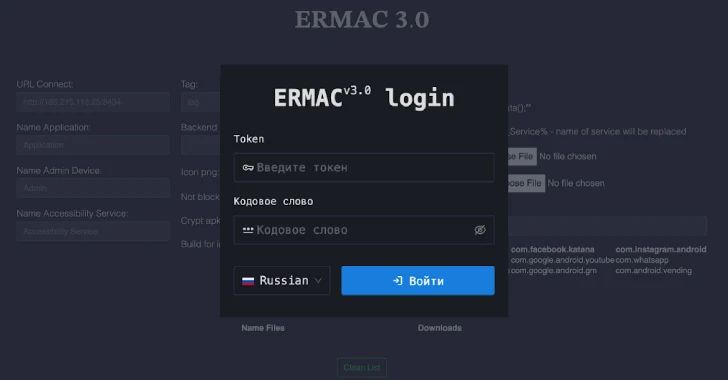
ERMAC V3.0 Banking Trojan Source Code Leak Exposes Full Malware Infrastructure