The Latest
-
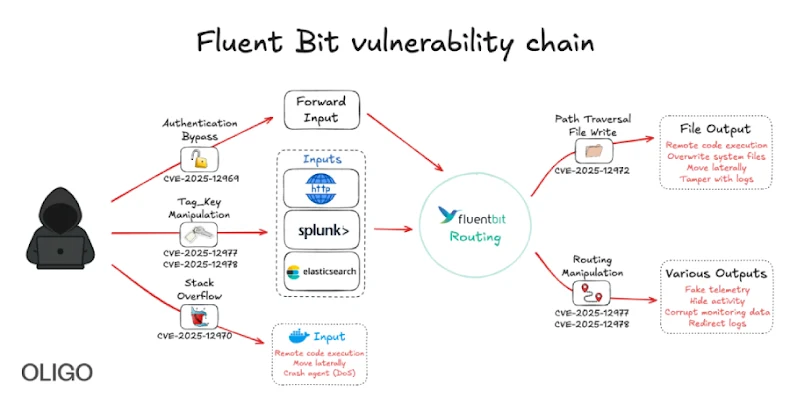
New Fluent Bit Flaws Expose Cloud to RCE and Stealthy Infrastructure Intrusions
-
⚡ Weekly Recap: Fortinet Exploit, Chrome 0-Day, BadIIS Malware, Record DDoS, SaaS Breach & More
-
Second Sha1-Hulud Wave Affects 25,000+ Repositories via npm Preinstall Credential Theft
-
Chinese DeepSeek-R1 AI Generates Insecure Code When Prompts Mention Tibet or Uyghurs