The Latest
-
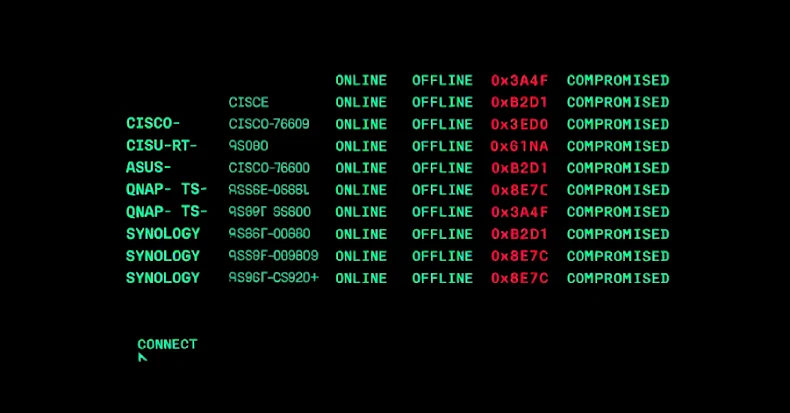
PolarEdge Targets Cisco, ASUS, QNAP, Synology Routers in Expanding Botnet Campaign
-
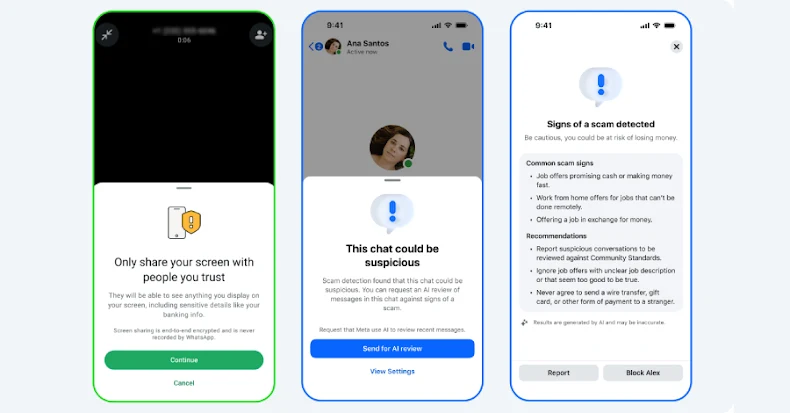
Meta Rolls Out New Tools to Protect WhatsApp and Messenger Users from Scams
-
Securing AI to Benefit from AI
-
Hackers Used Snappybee Malware and Citrix Flaw to Breach European Telecom Network