The Latest
-
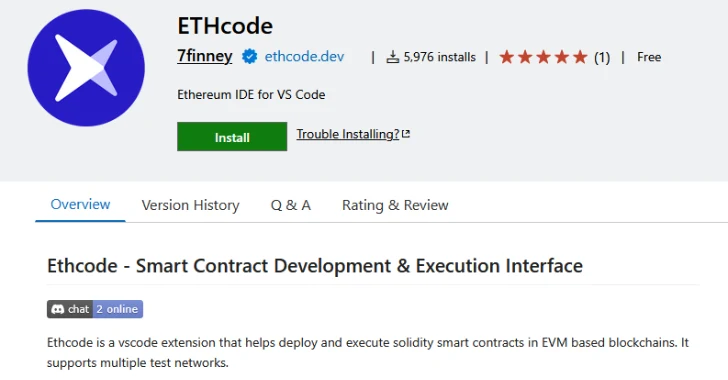
Malicious Pull Request Targets 6,000+ Developers via Vulnerable Ethcode VS Code Extension
-
BaitTrap: Over 17,000 Fake News Websites Caught Fueling Investment Fraud Globally
-
RondoDox Botnet Exploits Flaws in TBK DVRs and Four-Faith Routers to Launch DDoS Attacks
-
5 Ways Identity-based Attacks Are Breaching Retail