The Latest
-
SonicWall Investigating Potential SSL VPN Zero-Day After 20+ Targeted Attacks Reported
-
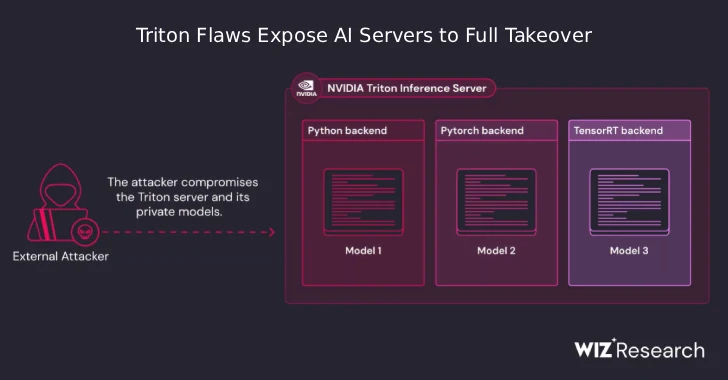
NVIDIA Triton Bugs Let Unauthenticated Attackers Execute Code and Hijack AI Servers
-
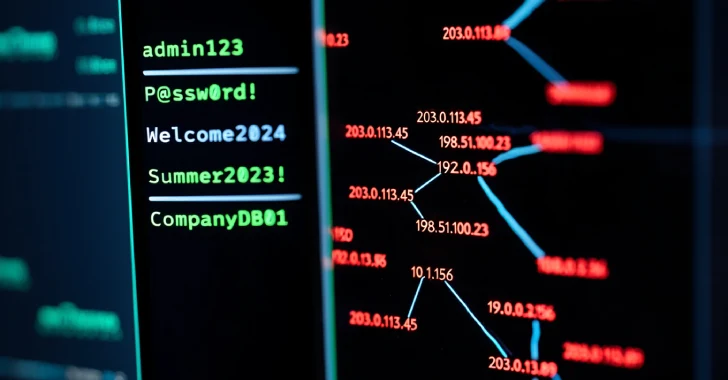
Vietnamese Hackers Use PXA Stealer, Hit 4,000 IPs and Steal 200,000 Passwords Globally
-
Man-in-the-Middle Attack Prevention Guide