The Latest
-
⚡ Weekly Recap: WhatsApp Worm, Critical CVEs, Oracle 0-Day, Ransomware Cartel & More
-
Why Unmonitored JavaScript Is Your Biggest Holiday Security Risk
-
Microsoft Locks Down IE Mode After Hackers Turned Legacy Feature Into Backdoor
-
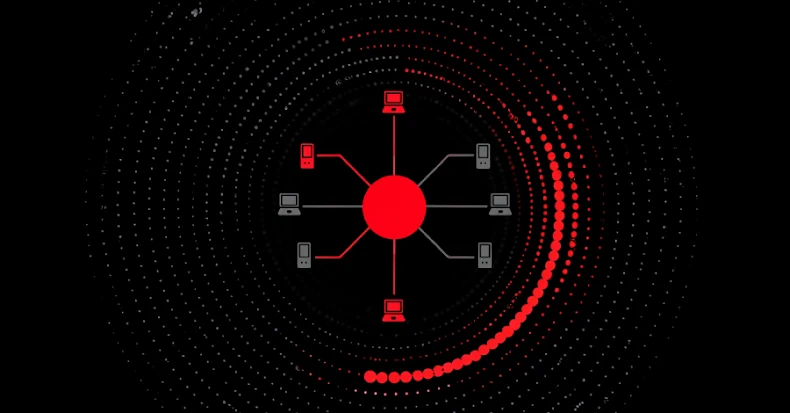
Researchers Warn RondoDox Botnet is Weaponizing Over 50 Flaws Across 30+ Vendors