The Latest
-
CISA Warns of Actively Exploited Critical Oracle Identity Manager Zero-Day Vulnerability
-
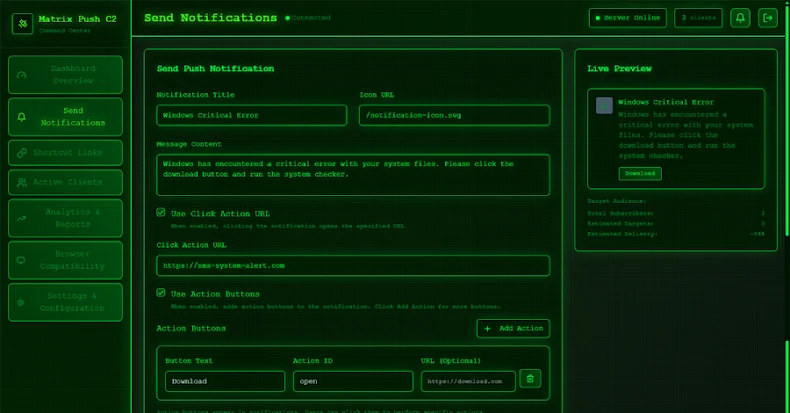
Matrix Push C2 Uses Browser Notifications for Fileless, Cross-Platform Phishing Attacks
-
Grafana Patches CVSS 10.0 SCIM Flaw Enabling Impersonation and Privilege Escalation
-
Google Brings AirDrop Compatibility to Android’s Quick Share Using Rust-Hardened Security