The Latest
-
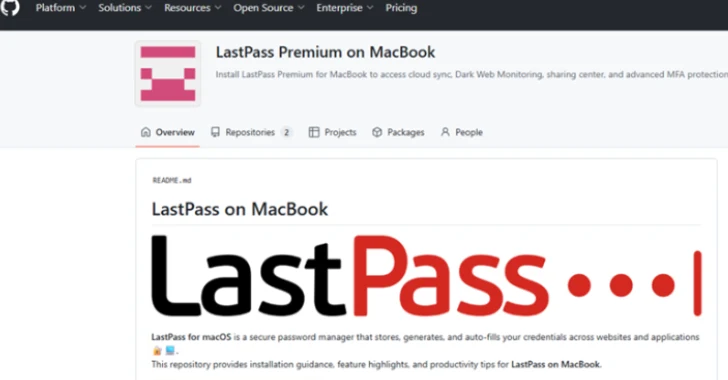
LastPass Warns of Fake Repositories Infecting macOS with Atomic Infostealer
-
Researchers Uncover GPT-4-Powered MalTerminal Malware Creating Ransomware, Reverse Shell
-
ShadowLeak Zero-Click Flaw Leaks Gmail Data via OpenAI ChatGPT Deep Research Agent
-
UNC1549 Hacks 34 Devices in 11 Telecom Firms via LinkedIn Job Lures and MINIBIKE Malware