The Latest
-
Google Identifies Three New Russian Malware Families Created by COLDRIVER Hackers
-
Five New Exploited Bugs Land in CISA's Catalog — Oracle and Microsoft Among Targets
-
131 Chrome Extensions Caught Hijacking WhatsApp Web for Massive Spam Campaign
-
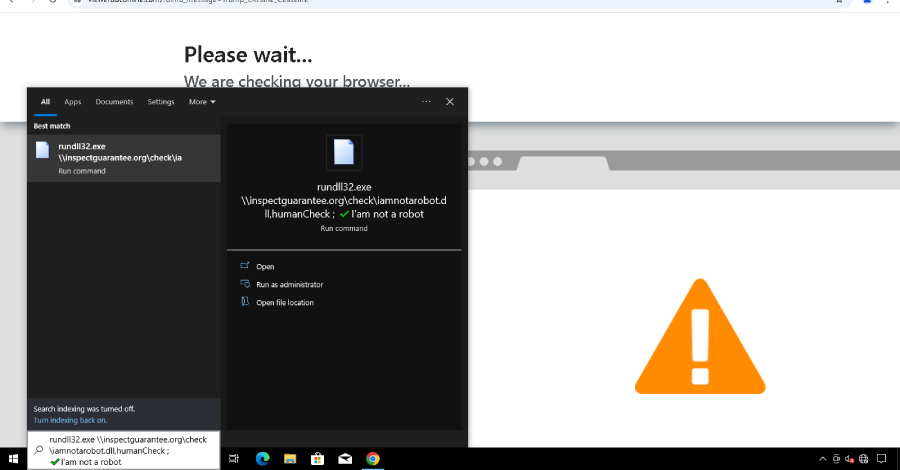
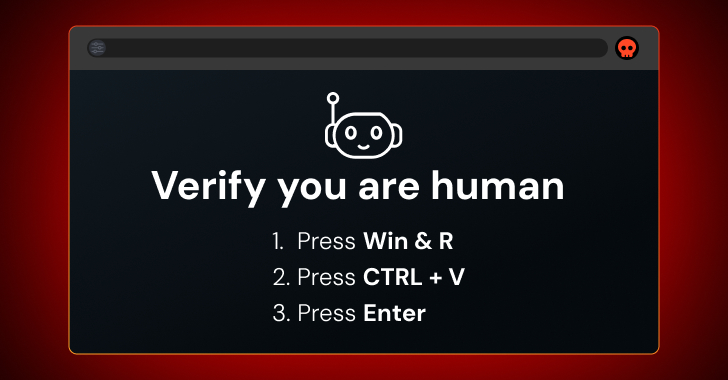
Analysing ClickFix: 3 Reasons Why Copy/Paste Attacks Are Driving Security Breaches