The Latest
-
Researchers Warn of MystRodX Backdoor Using DNS and ICMP Triggers for Stealthy Control
-
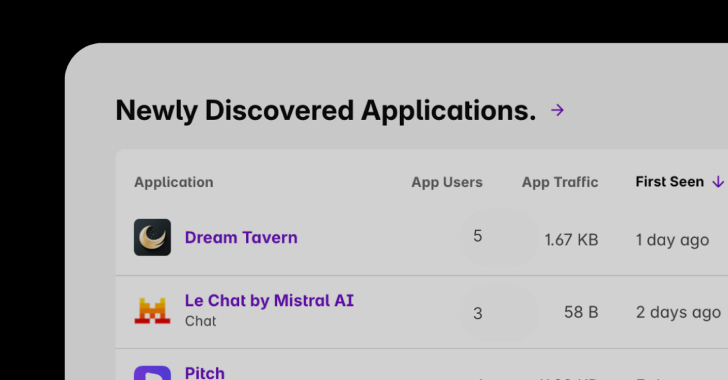
Shadow AI Discovery: A Critical Part of Enterprise AI Governance
-
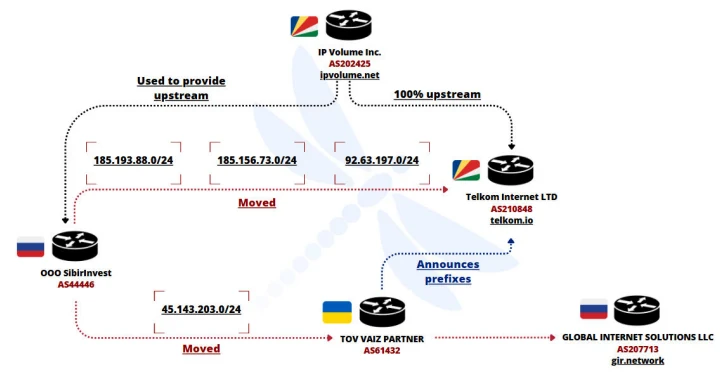
Ukrainian Network FDN3 Launches Massive Brute-Force Attacks on SSL VPN and RDP Devices
-
Silver Fox Exploits Microsoft-Signed WatchDog Driver to Deploy ValleyRAT Malware