The Latest
-
ShadowV2 Botnet Exploits Misconfigured AWS Docker Containers for DDoS-for-Hire Service
-
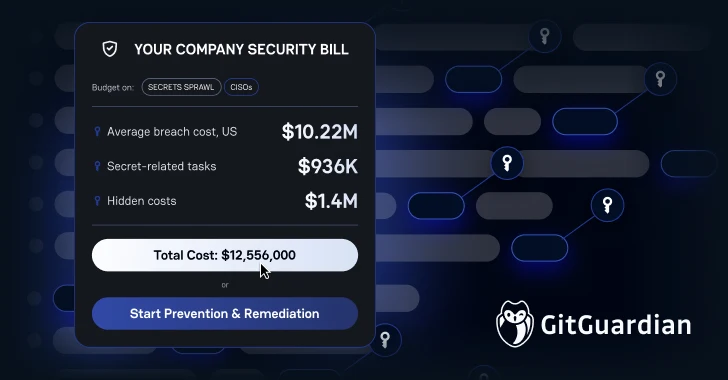
Lean Teams, Higher Stakes: Why CISOs Must Rethink Incident Remediation
-
GitHub Mandates 2FA and Short-Lived Tokens to Strengthen npm Supply Chain Security
-
BadIIS Malware Spreads via SEO Poisoning — Redirects Traffic, Plants Web Shells