The Latest
-
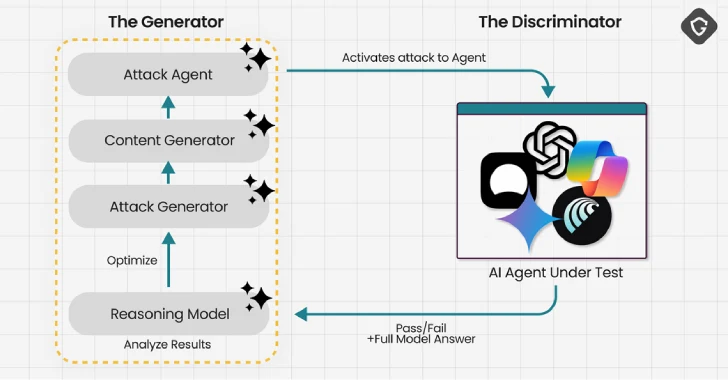
Experts Find AI Browsers Can Be Tricked by PromptFix Exploit to Run Malicious Hidden Prompts
-
🕵️ Webinar: Discover and Control Shadow AI Agents in Your Enterprise Before Hackers Do
-
From Impact to Action: Turning BIA Insights Into Resilient Recovery
-
North Korea Uses GitHub in Diplomat Cyber Attacks as IT Worker Scheme Hits 320+ Firms