The Latest
-
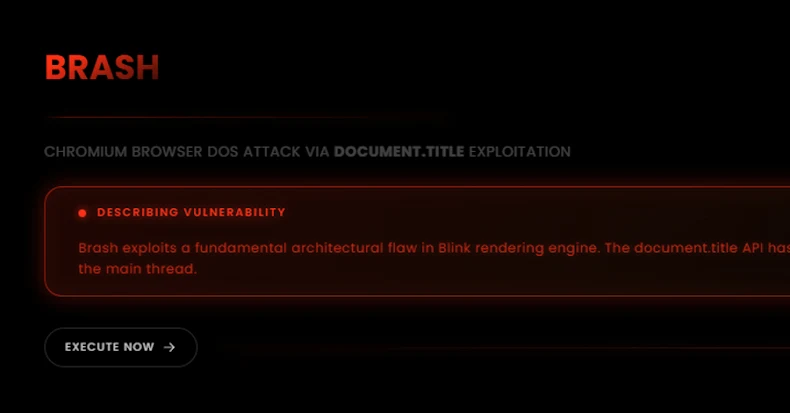
New "Brash" Exploit Crashes Chromium Browsers Instantly with a Single Malicious URL
-
The Death of the Security Checkbox: BAS Is the Power Behind Real Defense
-
PhantomRaven Malware Found in 126 npm Packages Stealing GitHub Tokens From Devs
-
ThreatsDay Bulletin: DNS Poisoning Flaw, Supply-Chain Heist, Rust Malware Trick and New RATs Rising