The Latest
-
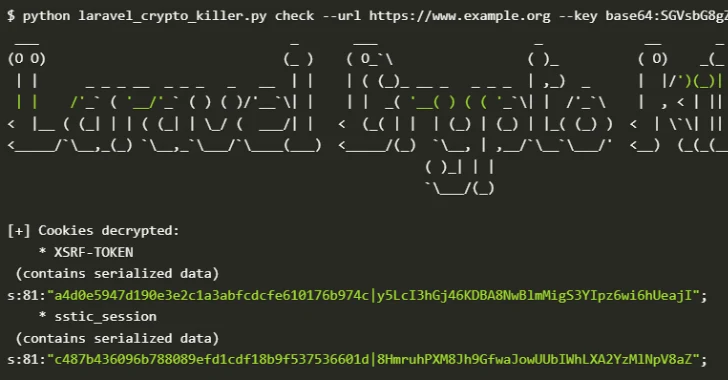
Over 600 Laravel Apps Exposed to Remote Code Execution Due to Leaked APP_KEYs on GitHub
-
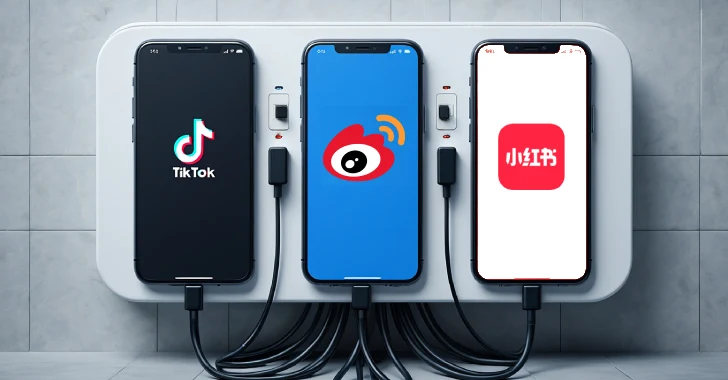
Taiwan NSB Alerts Public on Data Risks from Douyin, Weibo, and RedNote Over China Ties
-
Fortinet Releases Patch for Critical SQL Injection Flaw in FortiWeb (CVE-2025-25257)
-
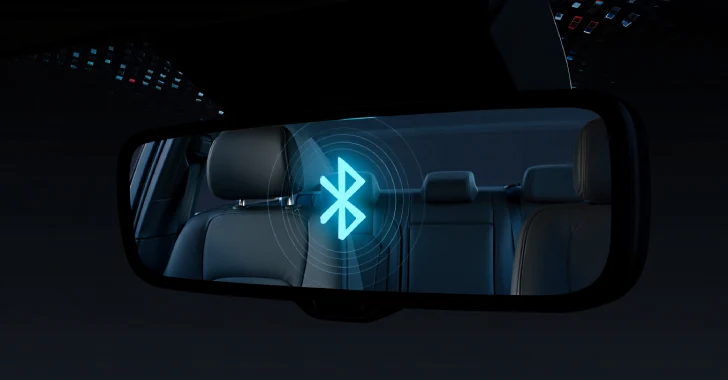
PerfektBlue Bluetooth Vulnerabilities Expose Millions of Vehicles to Remote Code Execution