The Latest
-
Android Trojan 'Fantasy Hub' Malware Service Turns Telegram Into a Hub for Hackers
-
Researchers Detect Malicious npm Package Targeting GitHub-Owned Repositories
-
CISO's Expert Guide To AI Supply Chain Attacks
-
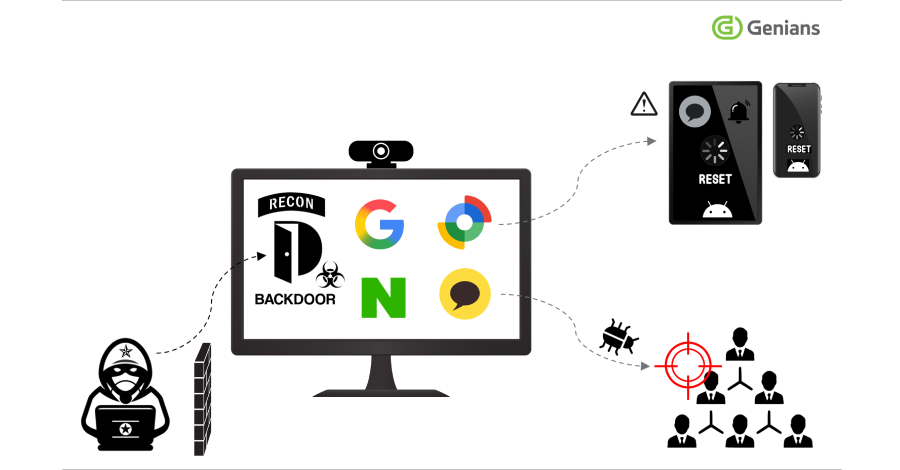
Konni Hackers Turn Google’s Find Hub into a Remote Data-Wiping Weapon