The Latest
-
Moving Beyond Awareness: How Threat Hunting Builds Readiness
-
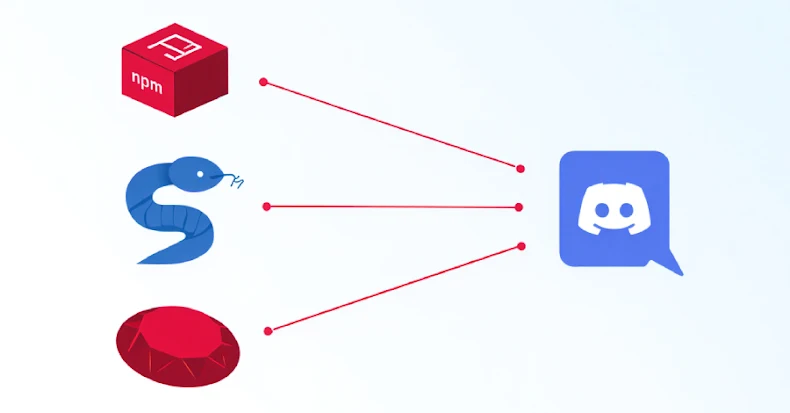
npm, PyPI, and RubyGems Packages Found Sending Developer Data to Discord Channels
-
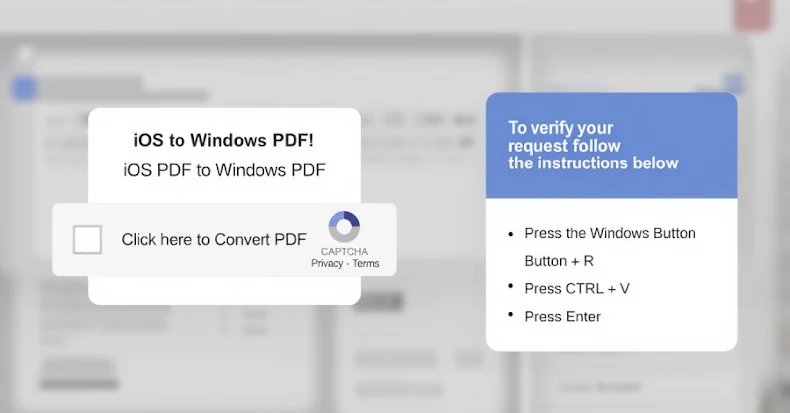
Researchers Expose TA585’s MonsterV2 Malware Capabilities and Attack Chain
-
⚡ Weekly Recap: WhatsApp Worm, Critical CVEs, Oracle 0-Day, Ransomware Cartel & More