The Latest
-
Watch This Webinar to Uncover Hidden Flaws in Login, AI, and Digital Trust — and Fix Them
-
Storm-2603 Exploits SharePoint Flaws to Deploy Warlock Ransomware on Unpatched Systems
-
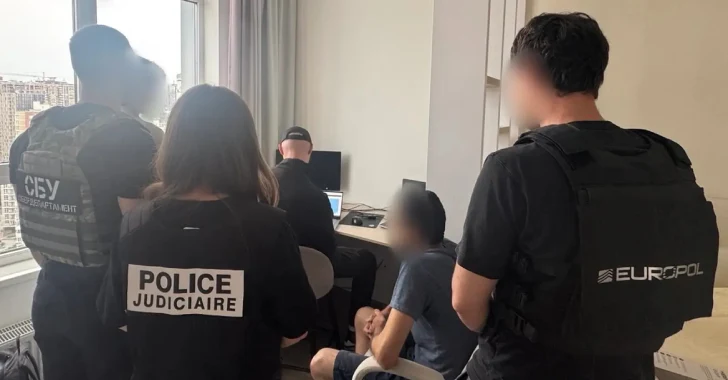
Europol Arrests XSS Forum Admin in Kyiv After 12-Year Run Operating Cybercrime Marketplace
-
Hackers Deploy Stealth Backdoor in WordPress Mu-Plugins to Maintain Admin Access