The Latest
-
Chrome Extension Caught Injecting Hidden Solana Transfer Fees Into Raydium Swaps
-
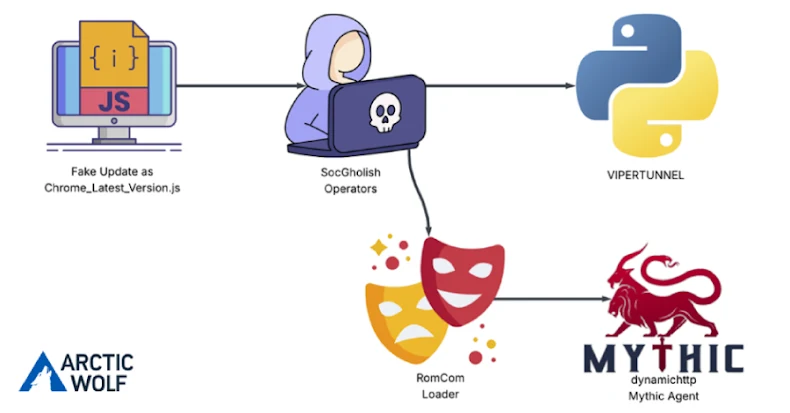
RomCom Uses SocGholish Fake Update Attacks to Deliver Mythic Agent Malware
-
FBI Reports $262M in ATO Fraud as Researchers Cite Growing AI Phishing and Holiday Scams
-
Years of JSONFormatter and CodeBeautify Leaks Expose Thousands of Passwords and API Keys