The Latest
-
AI Is Transforming Cybersecurity Adversarial Testing – Pentera Founder’s Vision
-
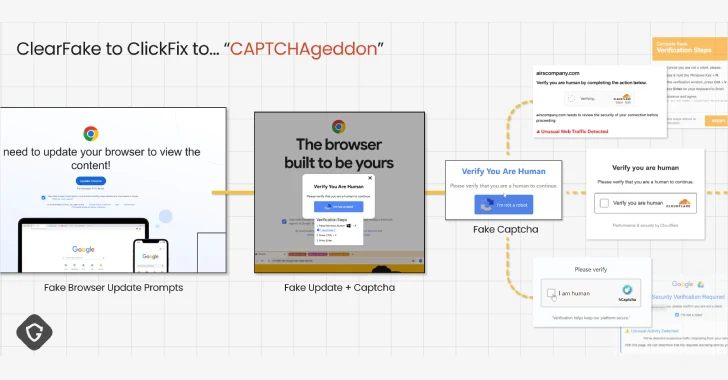
ClickFix Malware Campaign Exploits CAPTCHAs to Spread Cross-Platform Infections
-
Cursor AI Code Editor Vulnerability Enables RCE via Malicious MCP File Swaps Post Approval
-
Google’s August Patch Fixes Two Qualcomm Vulnerabilities Exploited in the Wild