The Latest
-
Iranian APT35 Hackers Targeting Israeli Tech Experts with AI-Powered Phishing Attacks
-
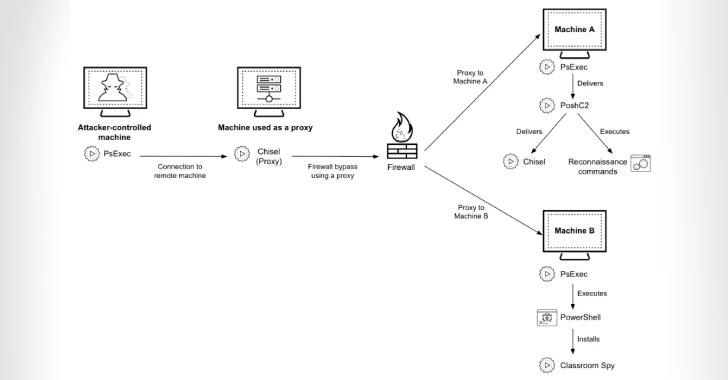
Cyber Criminals Exploit Open-Source Tools to Compromise Financial Institutions Across Africa
-
CISA Adds 3 Flaws to KEV Catalog, Impacting AMI MegaRAC, D-Link, Fortinet
-
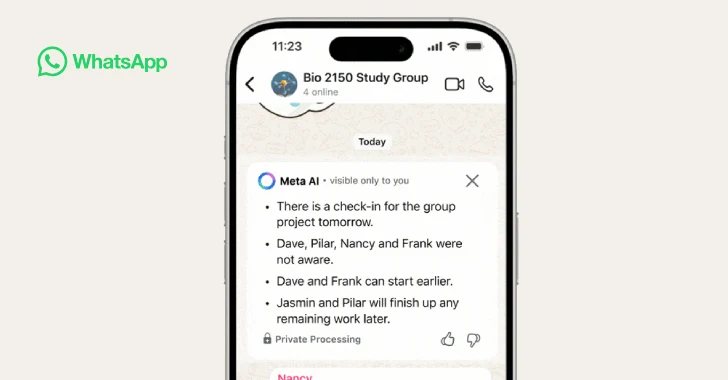
WhatsApp Adds AI-Powered Message Summaries for Faster Chat Previews