The Latest
-
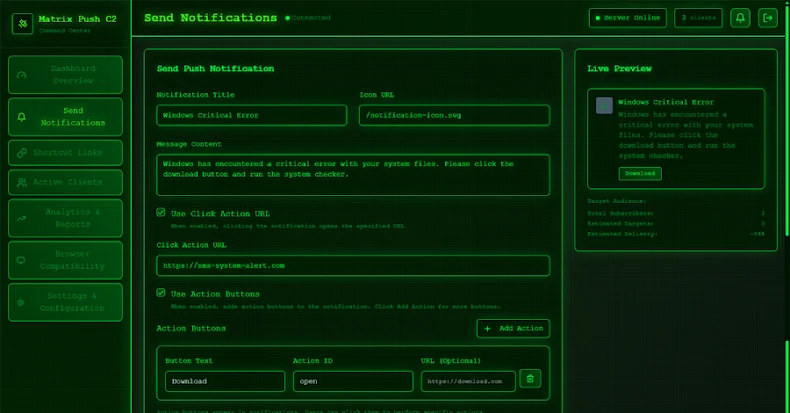
Matrix Push C2 Uses Browser Notifications for Fileless, Cross-Platform Phishing Attacks
-
Grafana Patches CVSS 10.0 SCIM Flaw Enabling Impersonation and Privilege Escalation
-
Google Brings AirDrop Compatibility to Android’s Quick Share Using Rust-Hardened Security
-
APT24 Deploys BADAUDIO in Years-Long Espionage Hitting Taiwan and 1,000+ Domains