The Latest
-
FedRAMP at Startup Speed: Lessons Learned
-
CISA Warns of Active Exploitation of Linux Kernel Privilege Escalation Vulnerability
-
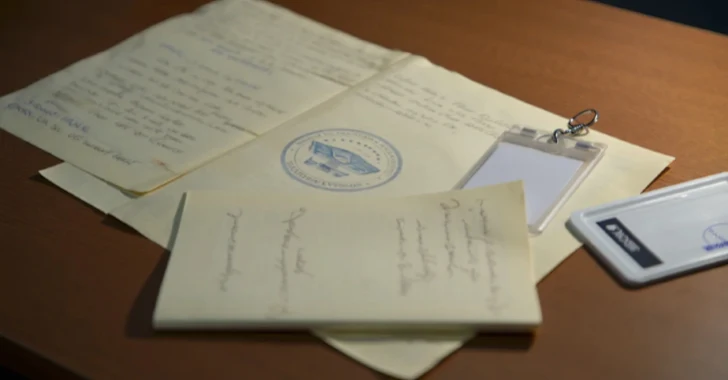
Ex-CIA Analyst Sentenced to 37 Months for Leaking Top Secret National Defense Documents
-
Iran Slows Internet to Prevent Cyber Attacks Amid Escalating Regional Conflict