The Latest
-
Apple Warns French Users of Fourth Spyware Campaign in 2025, CERT-FR Confirms
-
Samsung Fixes Critical Zero-Day CVE-2025-21043 Exploited in Android Attacks
-
Critical CVE-2025-5086 in DELMIA Apriso Actively Exploited, CISA Issues Warning
-
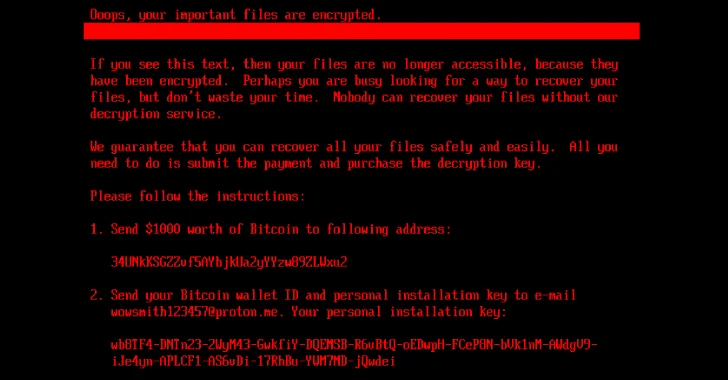
New HybridPetya Ransomware Bypasses UEFI Secure Boot With CVE-2024-7344 Exploit