The Latest
-
Hyper-Volumetric DDoS Attacks Reach Record 7.3 Tbps, Targeting Key Global Sectors
-
Newly Emerged GLOBAL GROUP RaaS Expands Operations with AI-Driven Negotiation Tools
-
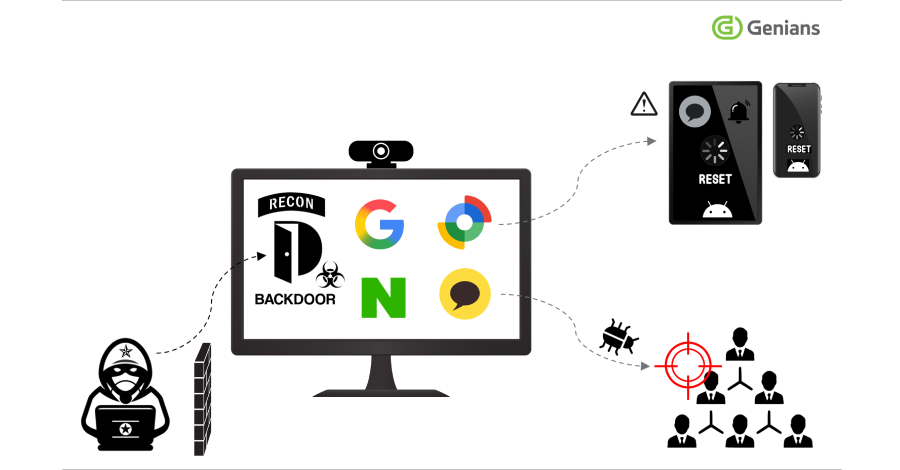
AsyncRAT's Open-Source Code Sparks Surge in Dangerous Malware Variants Across the Globe
-
Securing Agentic AI: How to Protect the Invisible Identity Access