The Latest
-
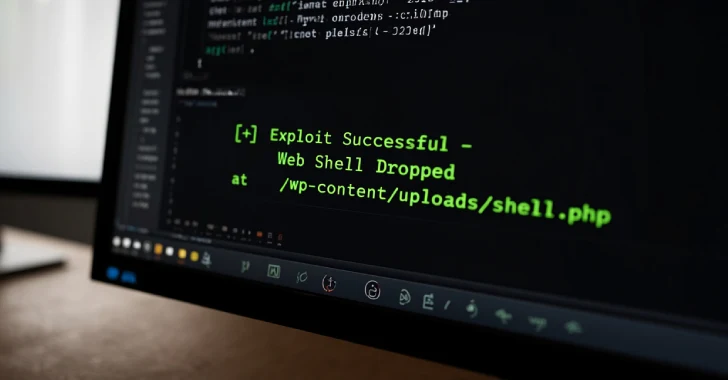
Hackers Exploit Critical WordPress Theme Flaw to Hijack Sites via Remote Plugin Install
-
Hackers Use Facebook Ads to Spread JSCEAL Malware via Fake Cryptocurrency Trading Apps
-
FunkSec Ransomware Decryptor Released Free to Public After Group Goes Dormant
-
Critical Dahua Camera Flaws Enable Remote Hijack via ONVIF and File Upload Exploits