The Latest
-
FBI Warns FSB-Linked Hackers Exploiting Unpatched Cisco Devices for Cyber Espionage
-
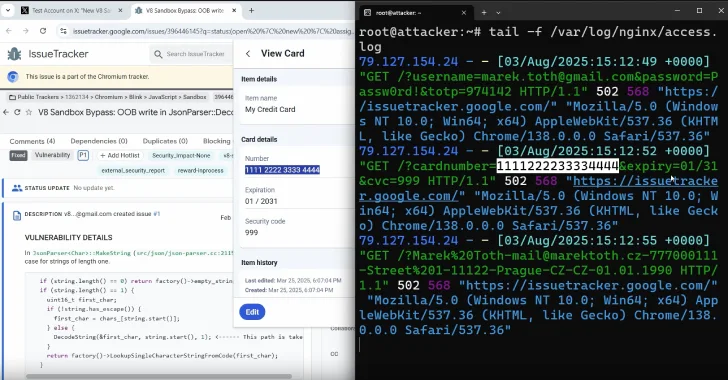
DOM-Based Extension Clickjacking Exposes Popular Password Managers to Credential and Data Theft
-
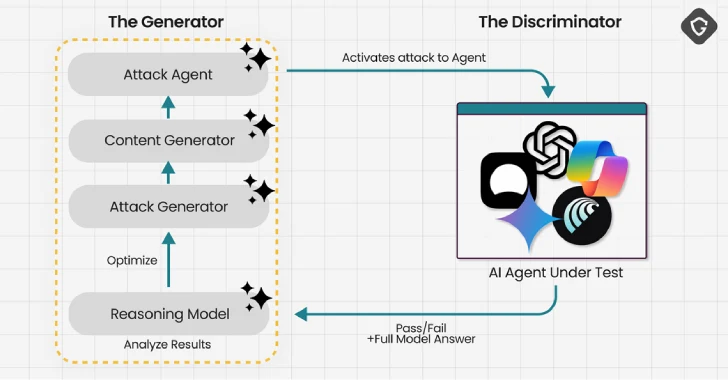
Experts Find AI Browsers Can Be Tricked by PromptFix Exploit to Run Malicious Hidden Prompts
-
🕵️ Webinar: Discover and Control Shadow AI Agents in Your Enterprise Before Hackers Do