The Latest
-
GreedyBear Steals $1M in Crypto Using 150+ Malicious Firefox Wallet Extensions
-
SocGholish Malware Spread via Ad Tools; Delivers Access to LockBit, Evil Corp, and Others
-
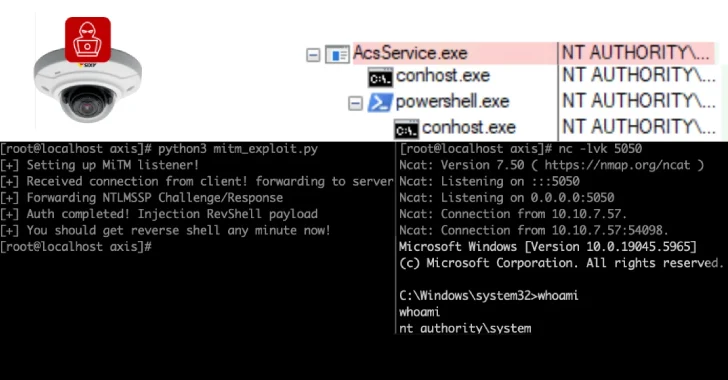
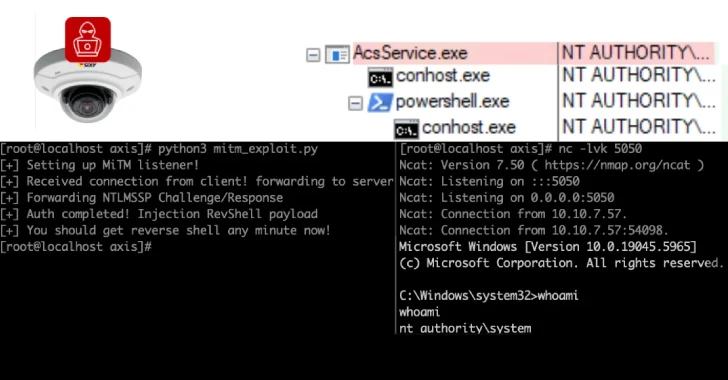
6,500 Axis Servers Expose Remoting Protocol; 4,000 in U.S. Vulnerable to Exploits
-
6,500 Axis Servers Expose Remoting Protocol, 4,000 in U.S. Vulnerable to Exploits